TL;DR: Scammers are exploiting Facebook’s “@highlight” feature to boost post reach and trick users. They post enticing images of prizes, prompting users to comment “@highlight,” which increases the post’s visibility. Once the post gains traction, scammers may edit it to include malicious links, leading to data harvesting, account takeover, or malware distribution.
 | If you’ve been on Facebook lately, you’ve likely seen your friends tagging “@highlight” in the comment section of posts promising luxury SUVs, motorhomes, or massive cash prizes. The pitch is simple: “Type @, click the highlight, and if it turns blue, you’re entered.” |
| At Fortitude Cyber, we believe that awareness is the first line of defence. While these posts look like harmless fun, they are part of a calculated social engineering tactic known as Engagement Baiting, and they can lead to serious cybersecurity risks for you and your network. | 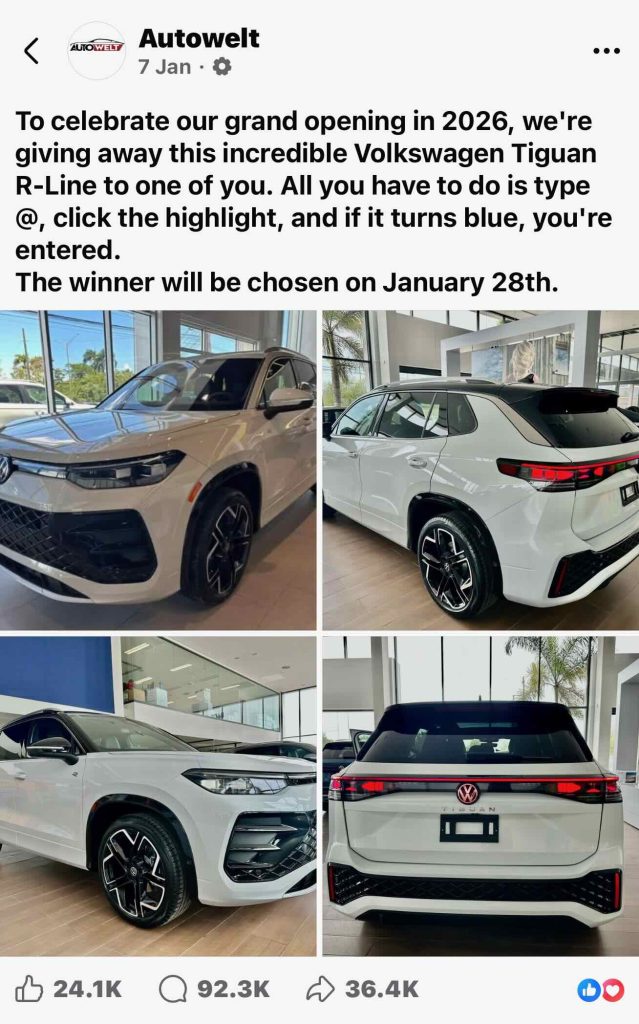 |
How the “@highlight” Scam Works
The “@highlight” feature is a legitimate Facebook tool designed for group admins to notify members of important updates. However, scammers are hijacking the concept to trick the algorithm and compromise users.
Here is the lifecycle of the scam:
- The Hook: A page (often with a generic name like “Autowelt” or “Hello Camper”) posts high-quality images of an expensive prize.
- The Interaction: They ask you to type “@highlight.” When you do this, Facebook’s autocomplete often suggests the tag. When it turns blue, it gives the user a false sense of “success” or “validation” that they have been entered into a drawing.
- The Algorithm Boost: Each comment signals to Facebook that the post is “high value,” pushing it into the feeds of thousands of other people. This is why these posts often have 90k+ comments.
- The Payload: Once the post has massive reach, the scammers change the game. They may edit the post to include a malicious link, send you a direct message (DM) claiming you’ve “won” but need to pay a shipping fee, or direct you to a phishing site to “register” your details.
Why Is This Dangerous?
You might think, “It’s just a comment; what’s the harm?” From a cybersecurity perspective, the risks are significant:
- Data Harvesting: To “claim” your prize, you are often directed to a website that asks for your name, address, phone number, and even credit card details for “verification.”
- Account Takeover: Some of these links lead to fake Facebook login pages. If you enter your credentials, the scammer now has full access to your account.
- Identifying Vulnerable Targets: By interacting with the post, you are essentially raising your hand and telling scammers, “I am susceptible to social engineering.” This can land you on “sucker lists” used for more targeted phishing attacks via email or SMS.
- Malware Distribution: Clicking “verification links” can trigger drive-by downloads of malware or fleeceware onto your mobile device.
Red Flags to Look For
To stay safe, look for these common indicators of a giveaway scam:
- The Page is New: Check the “Page Transparency” section. Most scam pages were created just days or weeks ago.
- Unverified Accounts: Genuine brands like Volkswagen or major dealerships will have a blue “Verified” checkmark.
- Impossible Prizes: No company is giving away a £40,000 car simply for typing a comment.
- Grammar and Logic Errors: Note the first image in this post—it mentions a grand opening in 2026. Scammers often use future dates or awkward phrasing to bypass automated spam filters.
What Should You Do?
If you see these posts, do not comment.
1. Report the Post: Click the three dots in the top right corner and select “Report post” -> “Scam.”
2. Educate Your Network: If you see a friend has commented, send them a quick message to let them know it’s a known engagement scam.
3. Check Your Privacy Settings: Ensure your Facebook profile isn’t sharing too much public information that scammers can use to build a profile on you.
Conclusion
Cybercriminals don’t always need complex code to break into your life; sometimes, they just need a picture of a white SUV and a “Highlight” tag.
Stay vigilant, stay skeptical, and remember: if it seems too good to be true, it almost certainly is.